|
|
|
"Crack Me If You Can" - DEFCON 2010 |
|
Back to Top Contest Scores
"Eligible" means that a team has completed the Code: validation to prove that they have someone physically attending DEFCON and are eligible to win the prize. See the How to Register page for more info. Ping a human if you think you've submitted a Code: but didn't get credit. Total Cracked Per Hash Type
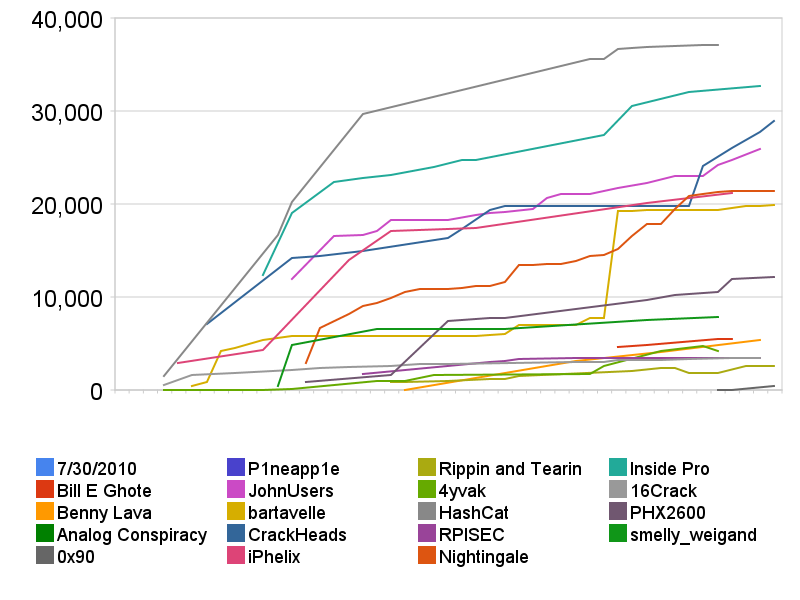
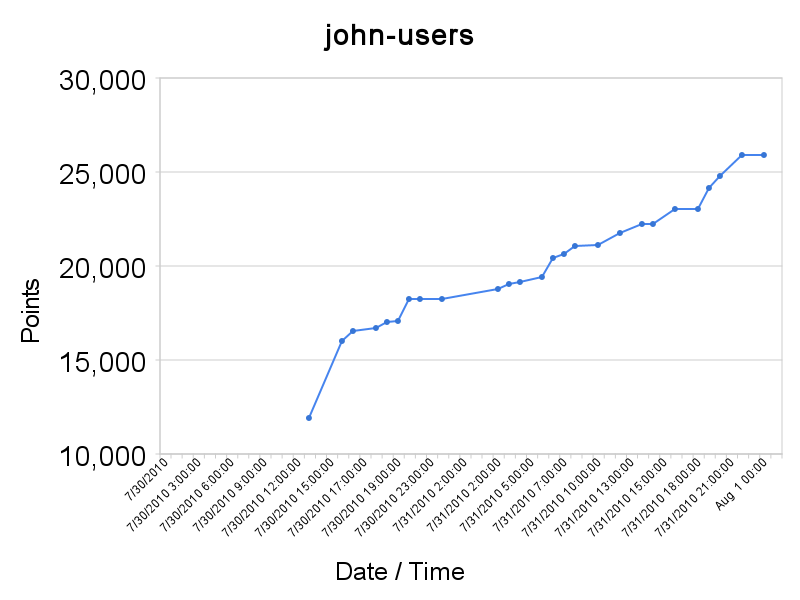
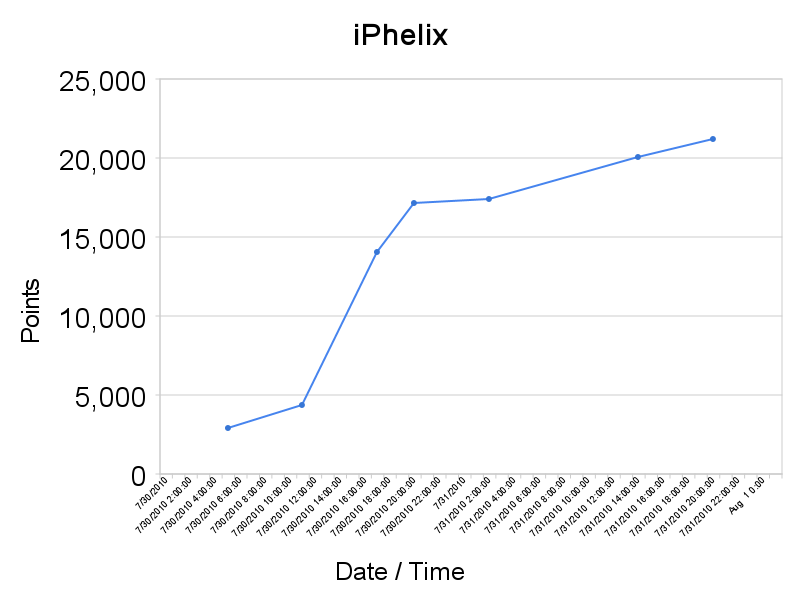
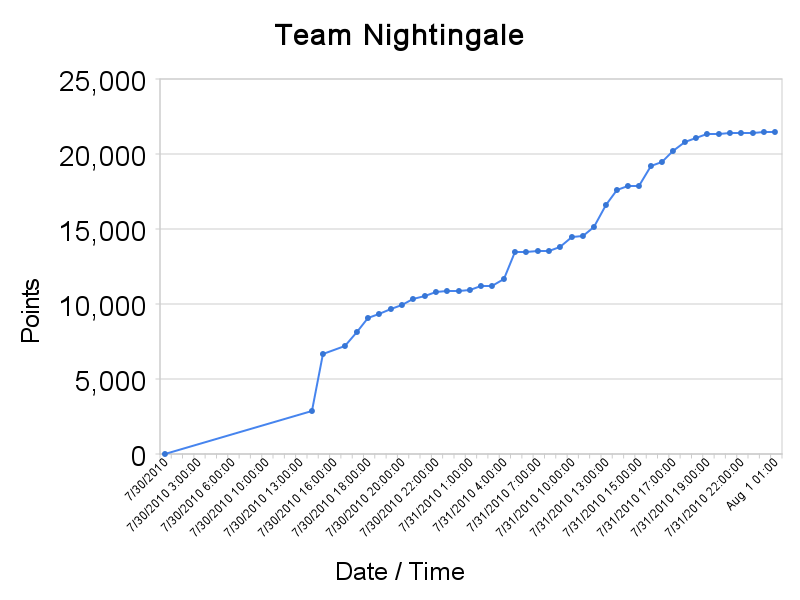
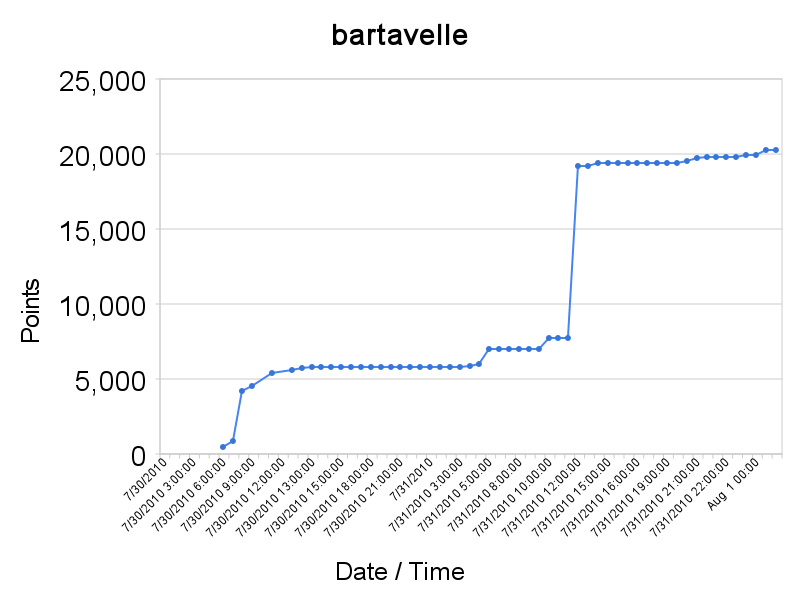
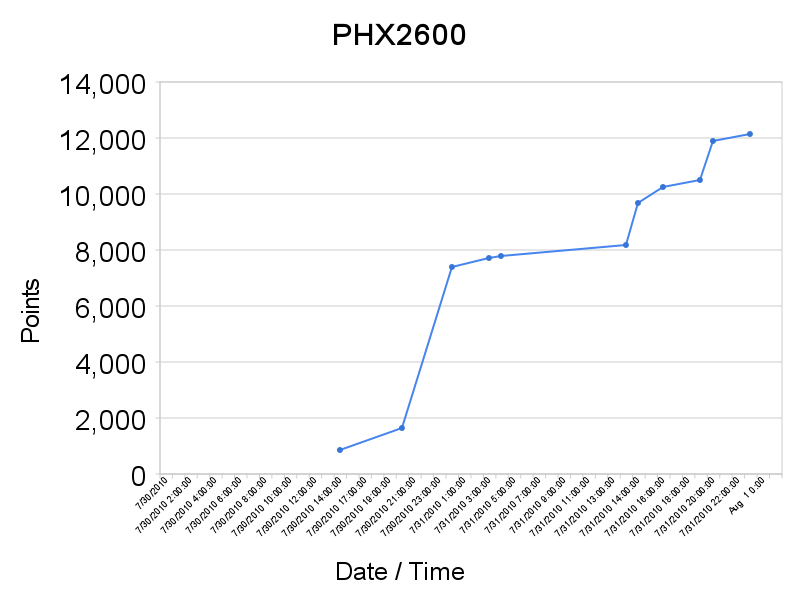
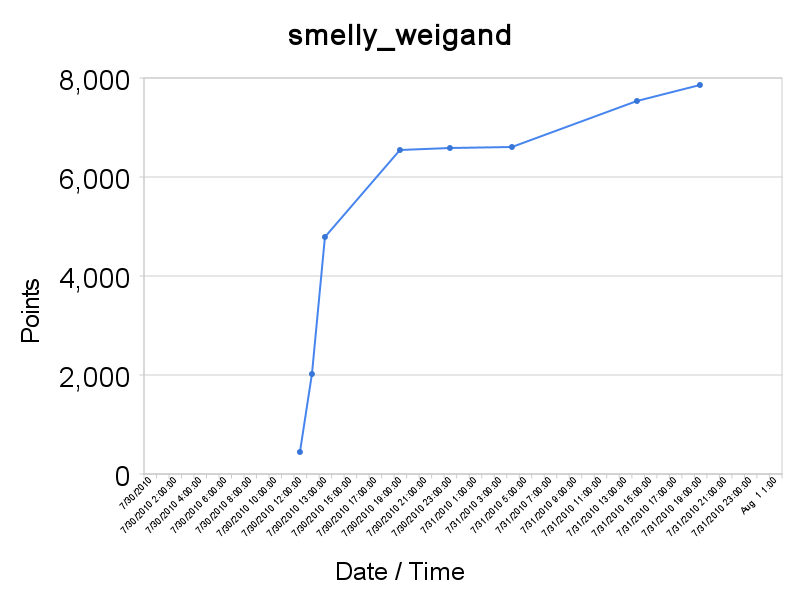
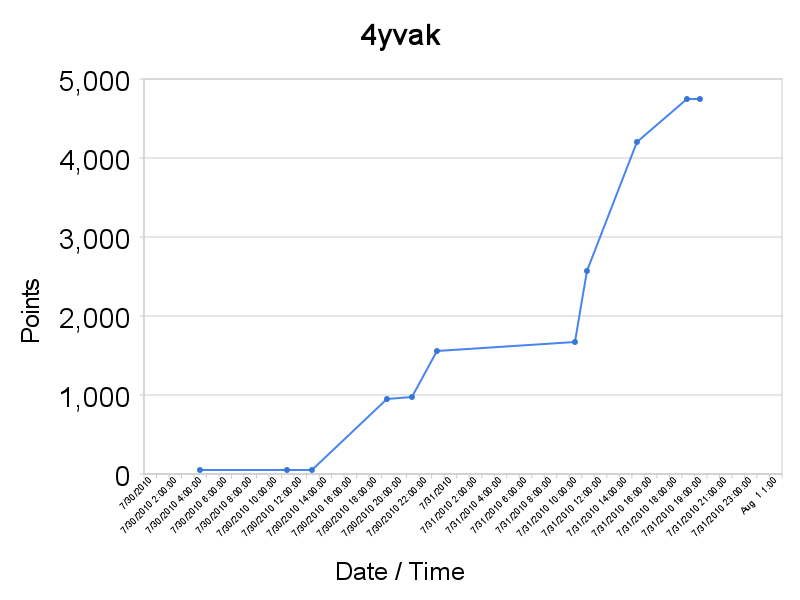
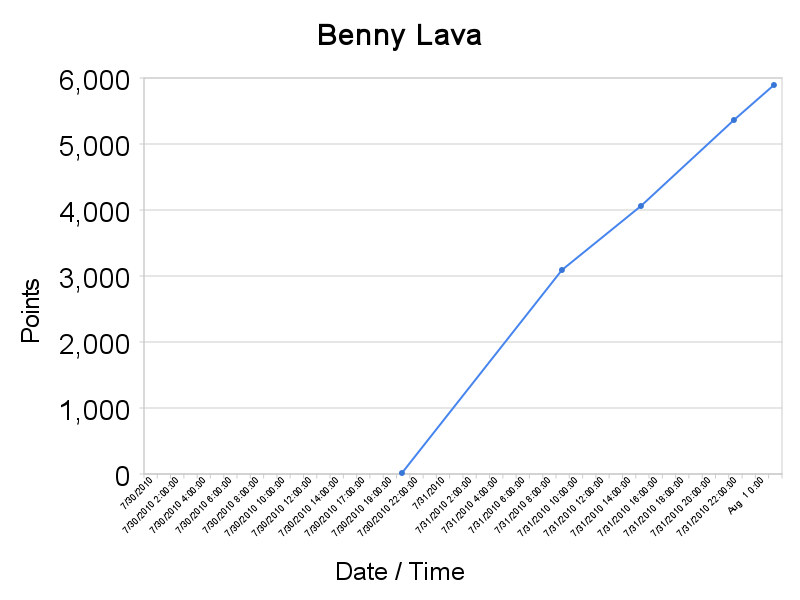
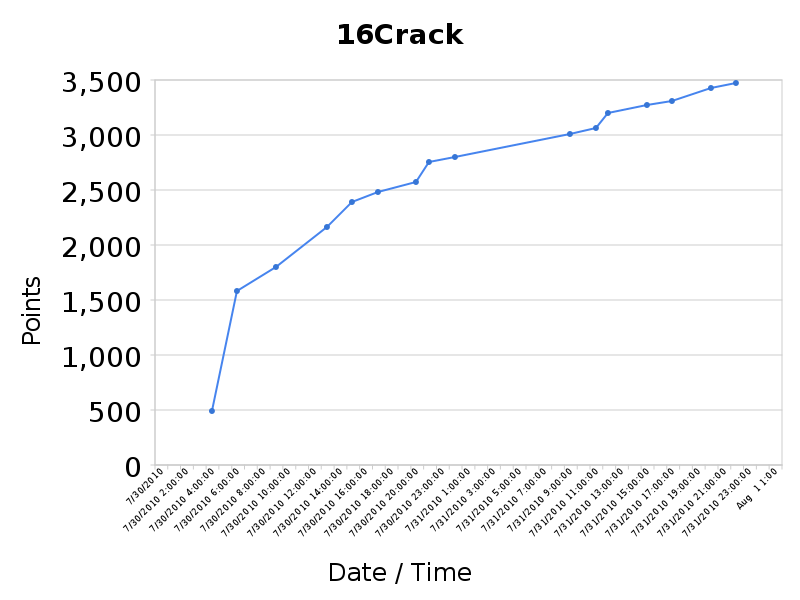
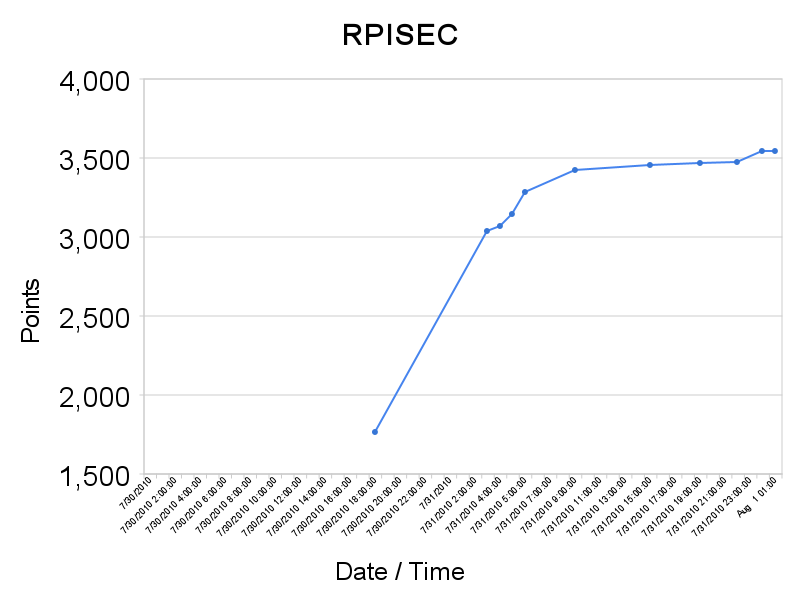
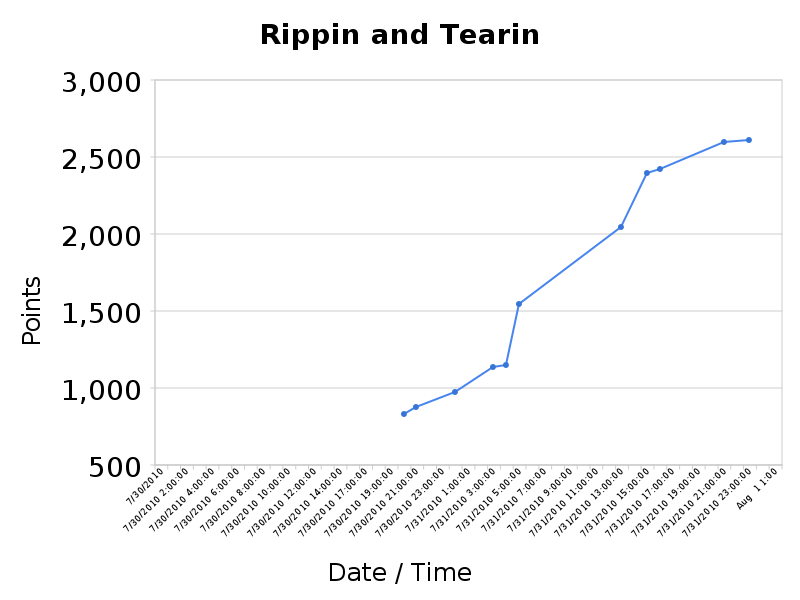
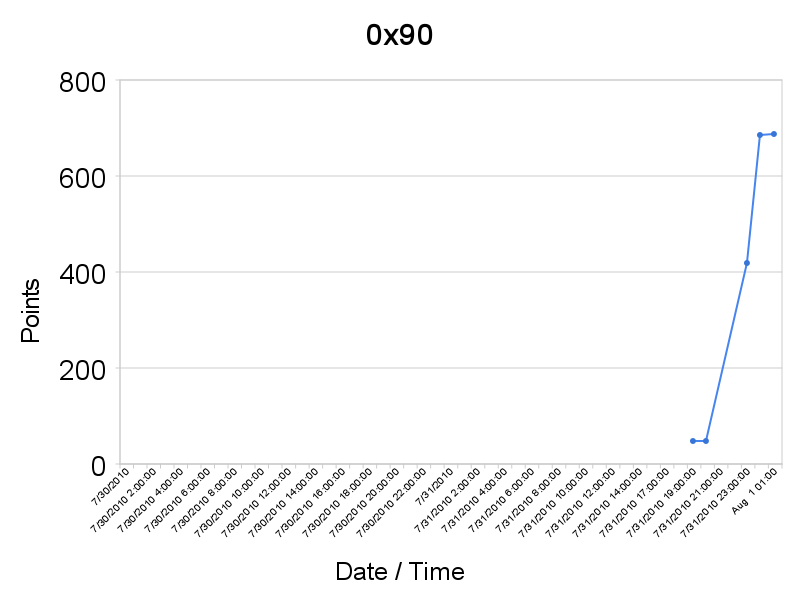
Team Cracks Over Time We intended that the passwords be roughly asymptotic in difficulty--so that many would crack fairly quickly at first, but they would get harder and harder (and thus crack slower) the more progress a team made. This seems to have pretty much worked as designed.
Here is a graph of all teams' crack performance over the life of the contest.
Note that many teams did not start right away, some as much as halfway through the competition.
(Yes, we ran out of good contrasting colors.) |
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Please contact us if you would like more information about our services, tools, or careers with us.
HOME : SOLUTIONS : RESULTS : TOOLS : RESOURCES : ABOUT KORELOGIC
Privacy Policy : Copyright 2025. KoreLogic Security. All rights reserved